Deep-dive into the Mango Markets economic attack


In light of the recent economic assault of the DeFi lending market, monitoring and managing risk has become a key factor for success within the ecosystem. Appropriate steps should be considered to ensure future growth of the space. The purpose of this article is to explore the recent Mango Markets economic attack, how it was organized, and possible mitigation strategies.
To understand how susceptible DeFi protocols are to certain types of risk, we dig into the 62 biggest incidents to date. This includes the hundreds of millions of dollars hacking of bridges, the economic collapse of algorithmic stablecoins, and the outright heist of user funds.
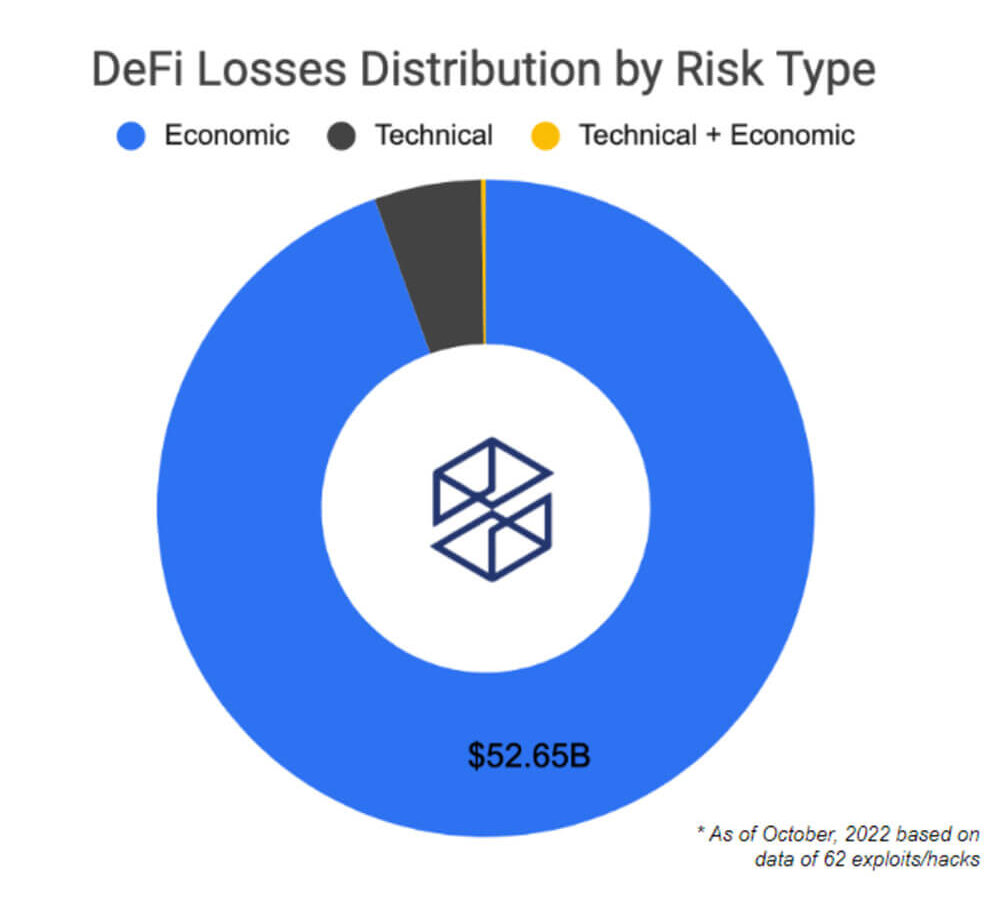
Here is the distribution of the main risk factors behind the 62 biggest DeFi attacks. Losses of over $50 billion are described as economic risks. This estimate includes the collapse of the infamous Terra ecosystem. Despite the technical factors behind the most attacks in DeFi, economic risks are actually wiping out more dollars in value.
Moreover, the recent series of economic attacks on several lending protocols such as Mango and Moola has exposed the danger this poses to the ecosystem. Additionally, many of these lending protocols were attacked using the same vector. The attack consisted of a highly complex strategy in which the attackers identified the underlying collateral assets with the lowest liquidity and market capitalization. Less liquid assets are most vulnerable to flash loans and price oracle manipulation attacks.

The above indicators are for educational purposes. For reference only, actual data is not shown. The DEX Pool Liquidity Indicator is part of a set of mockups built for the proposal euler forum.
By tracking the liquidity available for an asset on a decentralized exchange, we can measure how likely an asset is to be manipulated. A healthy level of available liquidity in the underlying collateral assets is an important safety factor. For less liquid tokens listed as collateral, there may be protocol stability issues. Additionally, this could facilitate an easier path for attackers to leverage the protocol to manipulate prices.
The main goal of attackers orchestrating this kind of attack is to increase the amount of money that can be borrowed. This can be done by pumping discovered less liquid assets so that they can borrow large amounts of other supported, more stable assets.

The graph above shows the price of the MNG token on the FTX exchange. In this case, the attacker combined the protocol’s lending functionality with a perpetual contract.of attacker Manipulated Raydium’s spot price that triggered an Oracle update. This allowed him to borrow against another open position he had previously placed on his Mango Markets protocol. Ultimately, the protocol remained in default when MNGO prices recovered.
Related to the above indicators of trying to find weak links in protocols, there are also methods of trying to find potential threats from the attacker’s side. Economic exploitation is usually carried out quickly. The indicators presented below are therefore useful for educational purposes when trying to assess potential threats from whale supply concentrations.
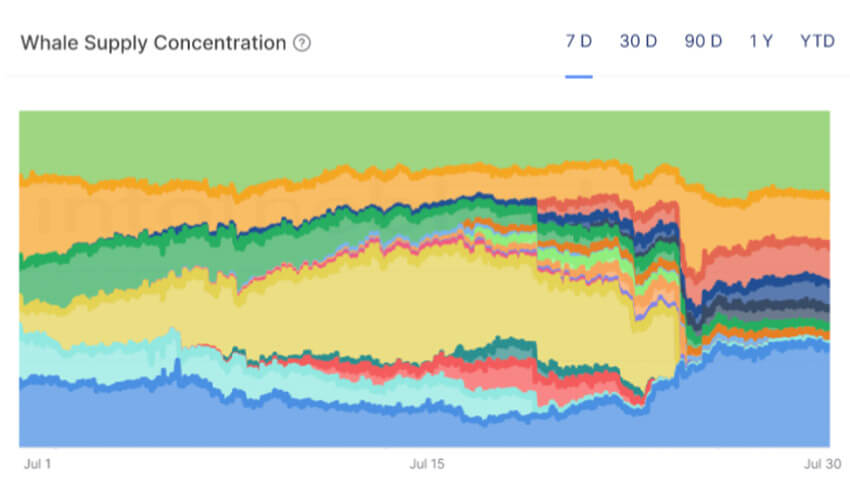
The Whale Supply Concentration Index also euler forumThis indicator helps identify potential threats to the protocol’s depositors. For example, if she, one of the largest protocol depositors, belongs to the least liquid assets that the protocol supports as collateral assets, then that particular address deserves further investigation.
This indicator is worth using in conjunction with the DEX Pool liquidity indicator above, and especially worth watching if the Concentrated Whale Token is one of the weakest tokens supported by the protocol. This helps shed light on possible adverse events.
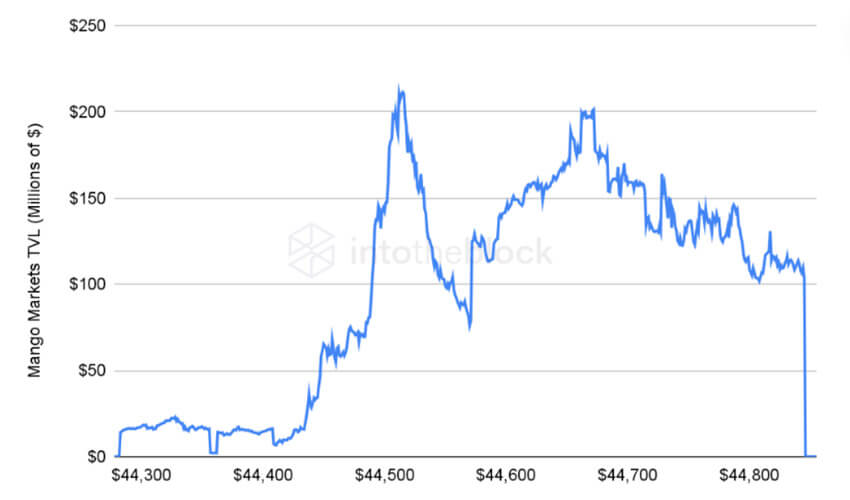
Mango Markets protocol TVL can be seen in the indicator above. A clear drop is seen after the attacker borrowed money against his MNGO token position. Ultimately, a price manipulation event left the protocol with bad debt.
The right tools like the ones above are meant to move the DeFi ecosystem one step in the right direction. These are just some of the initial indicators that first describe recent events and second try to protect users from such incidents in the future. The aim is for users and protocols to benefit from available on-chain information.





