Blockchain Security Alliance Q3 2022 Blockchain Security Report


1 A Brief Look at Blockchain Security in Q3 2022
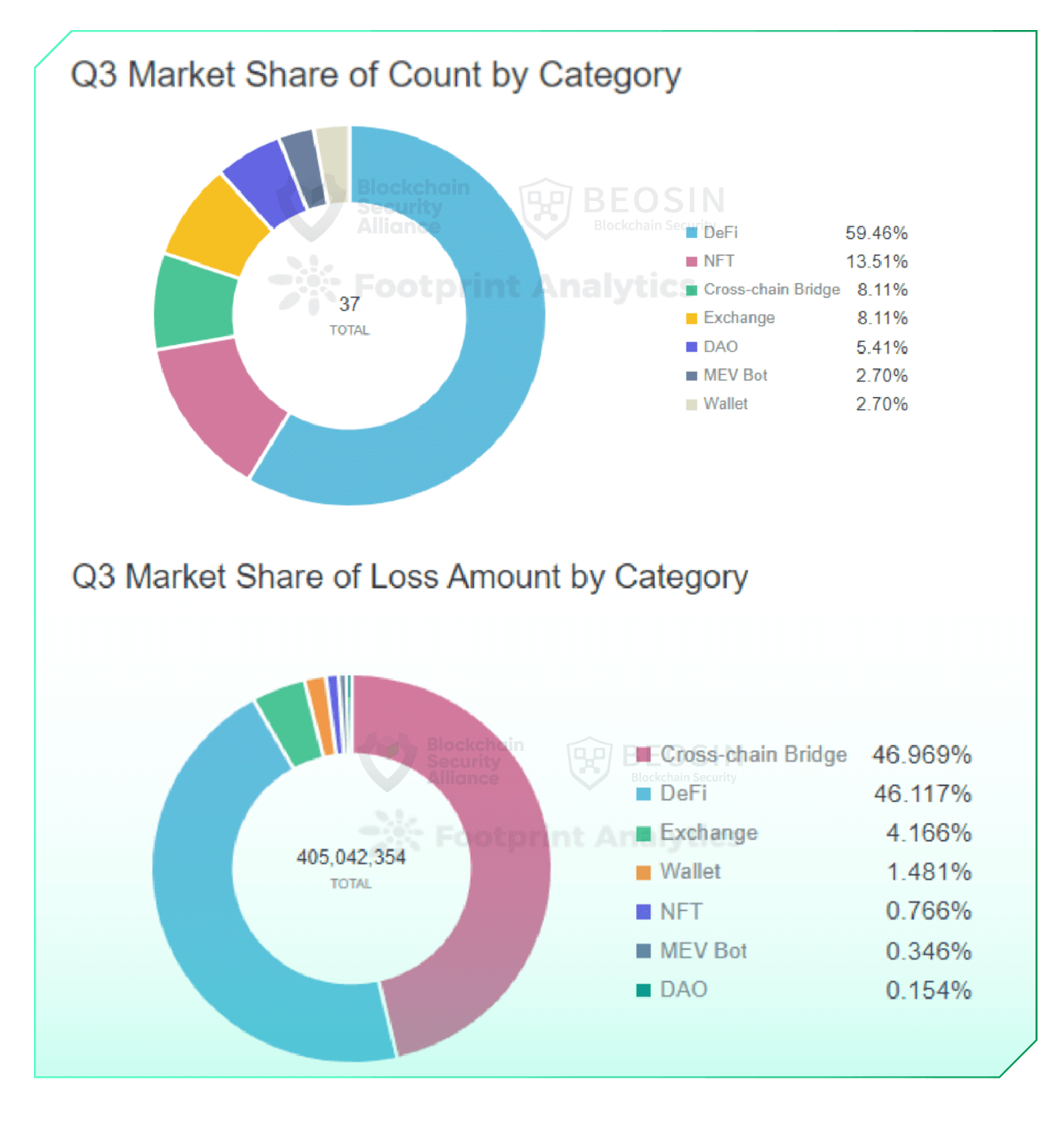
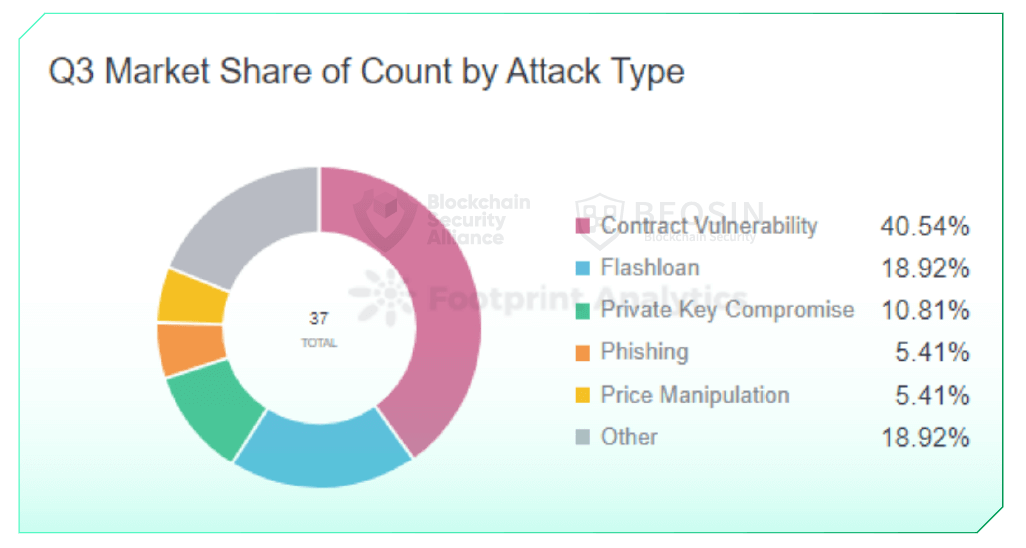
In total, 37 major exploits were monitored, resulting in a combined loss of approximately $405 million
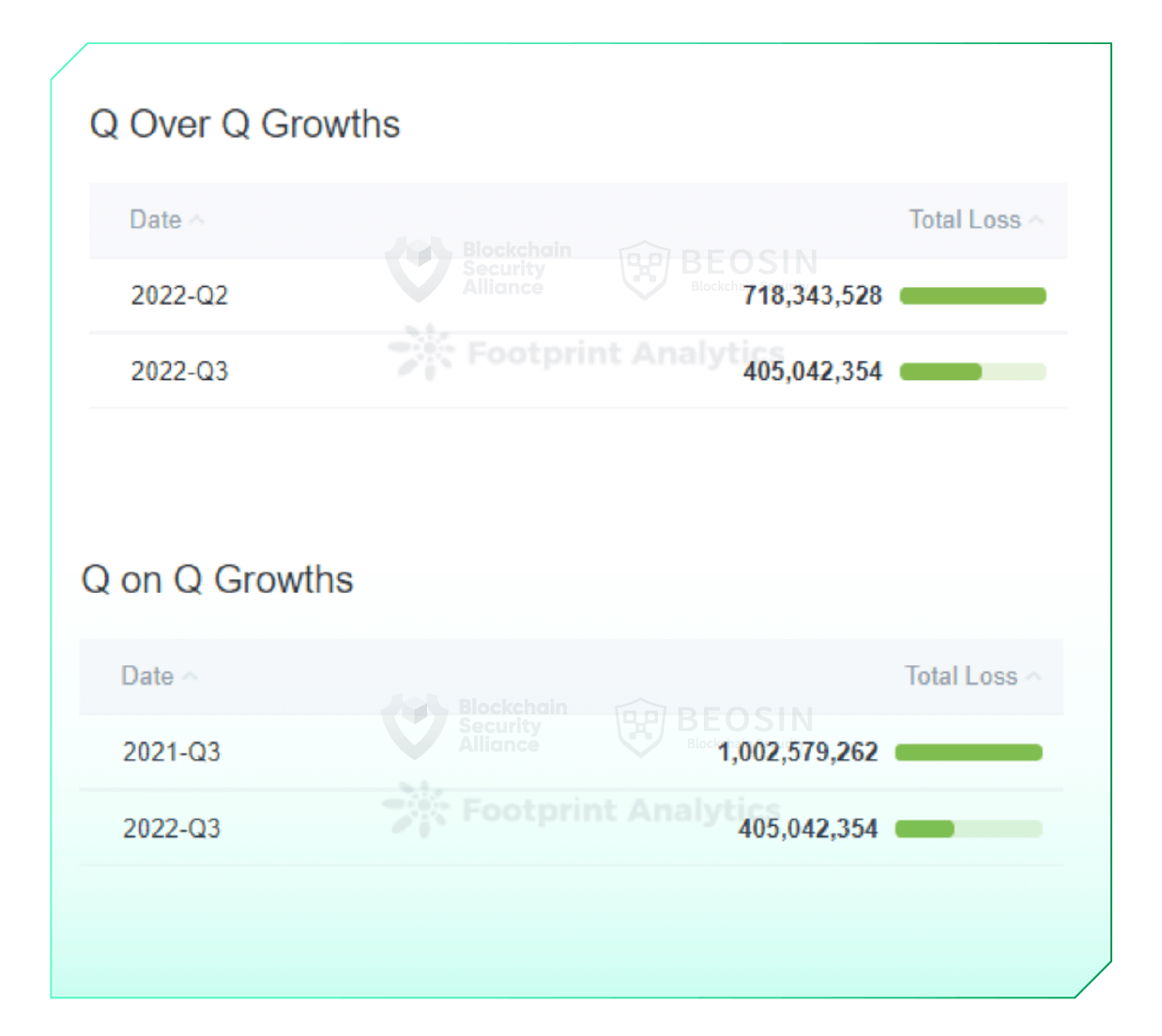
In Q3 2022, Beosin EagleEye monitored over 37 large-scale attacks in the Web3 space, resulting in total losses of approximately $405 million, down from $718.34 million in Q2 2022. It was down 43.6% and down 59.6% from a loss of $1,025.8 million in Q2 2022. Q3 2021.
From January to September 2022, assets lost in the Web3 space due to attacks totaled $2,317.91 million.
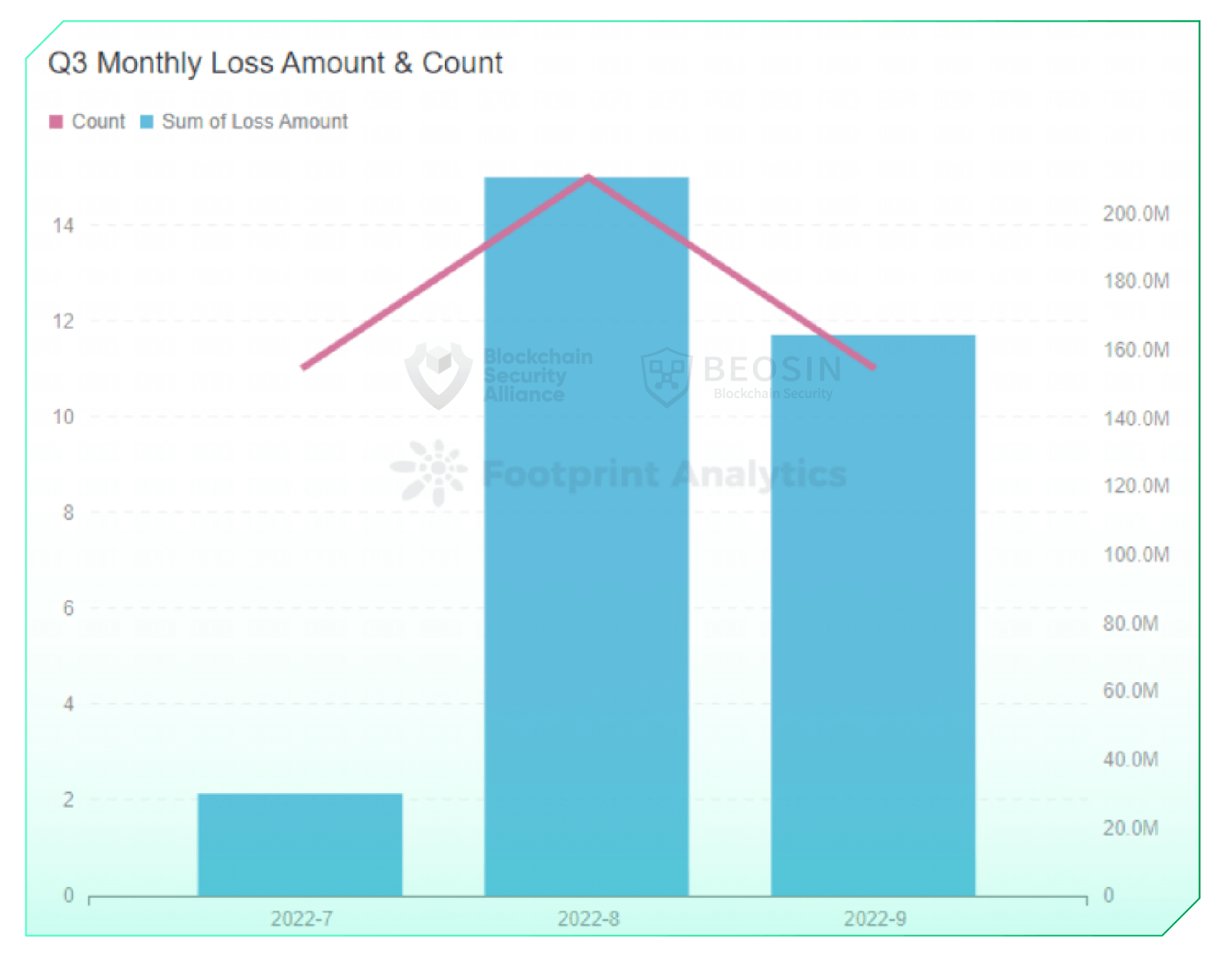
On a monthly basis, July saw a significant decline in attacks, resulting in the lowest amount of money lost to attacks since 2022. Hacker activity increased significantly in August and September.
About project types92% of the money lost came from cross-chain bridges and DeFi protocols, with 22 of the 37 attacks occurring in the DeFi space.
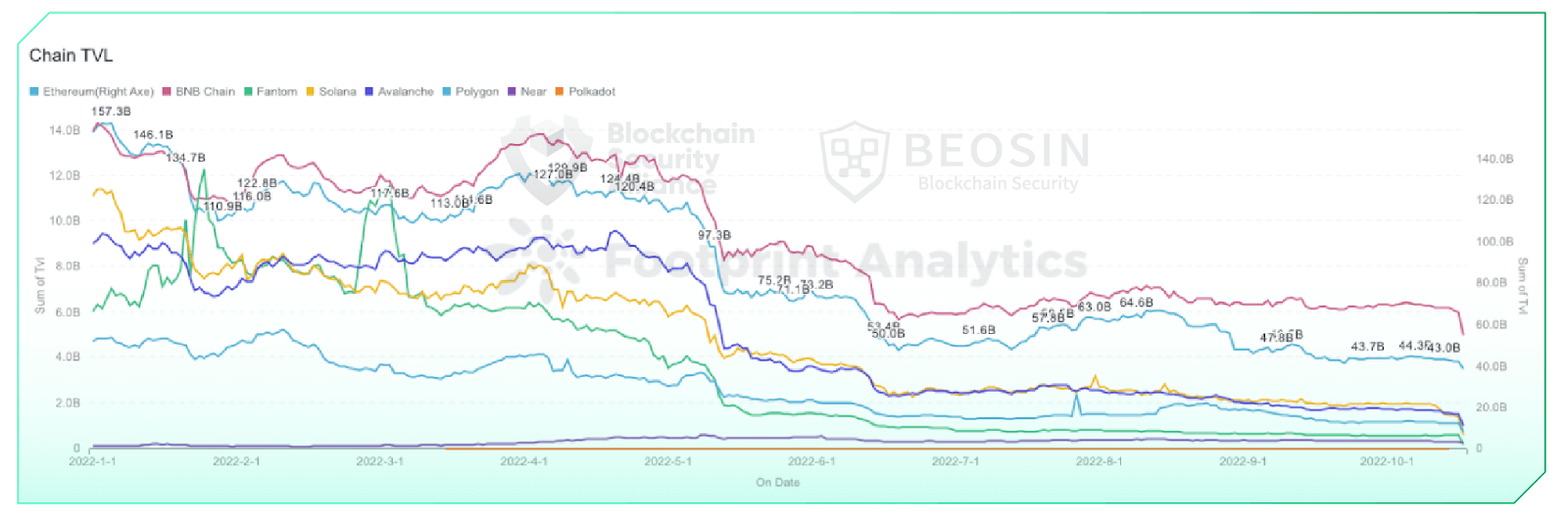
Regarding TVL, TVL trends tended to stabilize for each chain in the quarter after a significant drop in TVL from May to June. TVL was on a slight upward trend from late July to early August, when he had the highest number of attacks and losses during the quarter.
Regarding the chain Ethereum lost $374.28 million in the quarter, accounting for 92% of total losses. The most frequently attacked chain was his BNB chain, reaching 16 times.
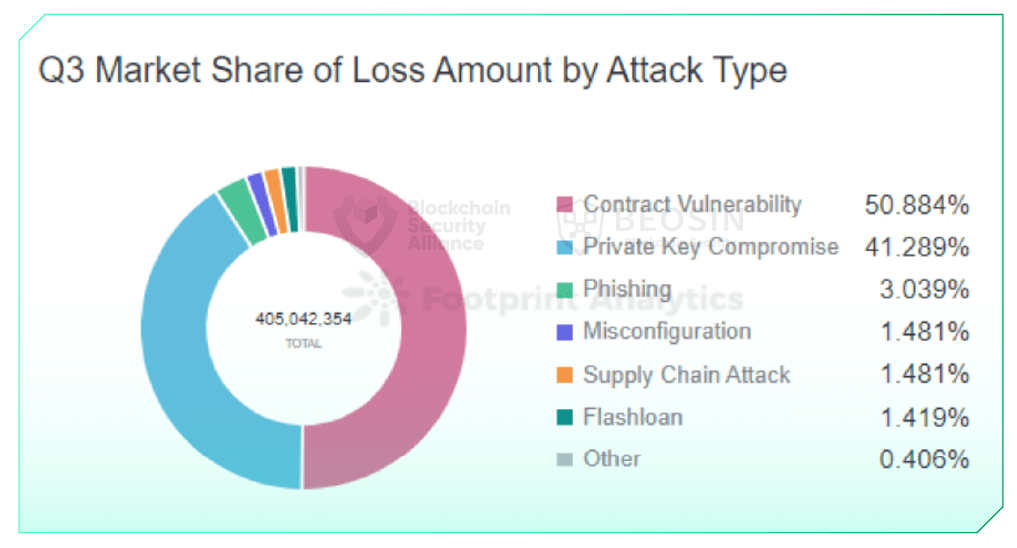
Regarding attack types, 92% of losses were due to contract vulnerability exploitation and private key compromise.
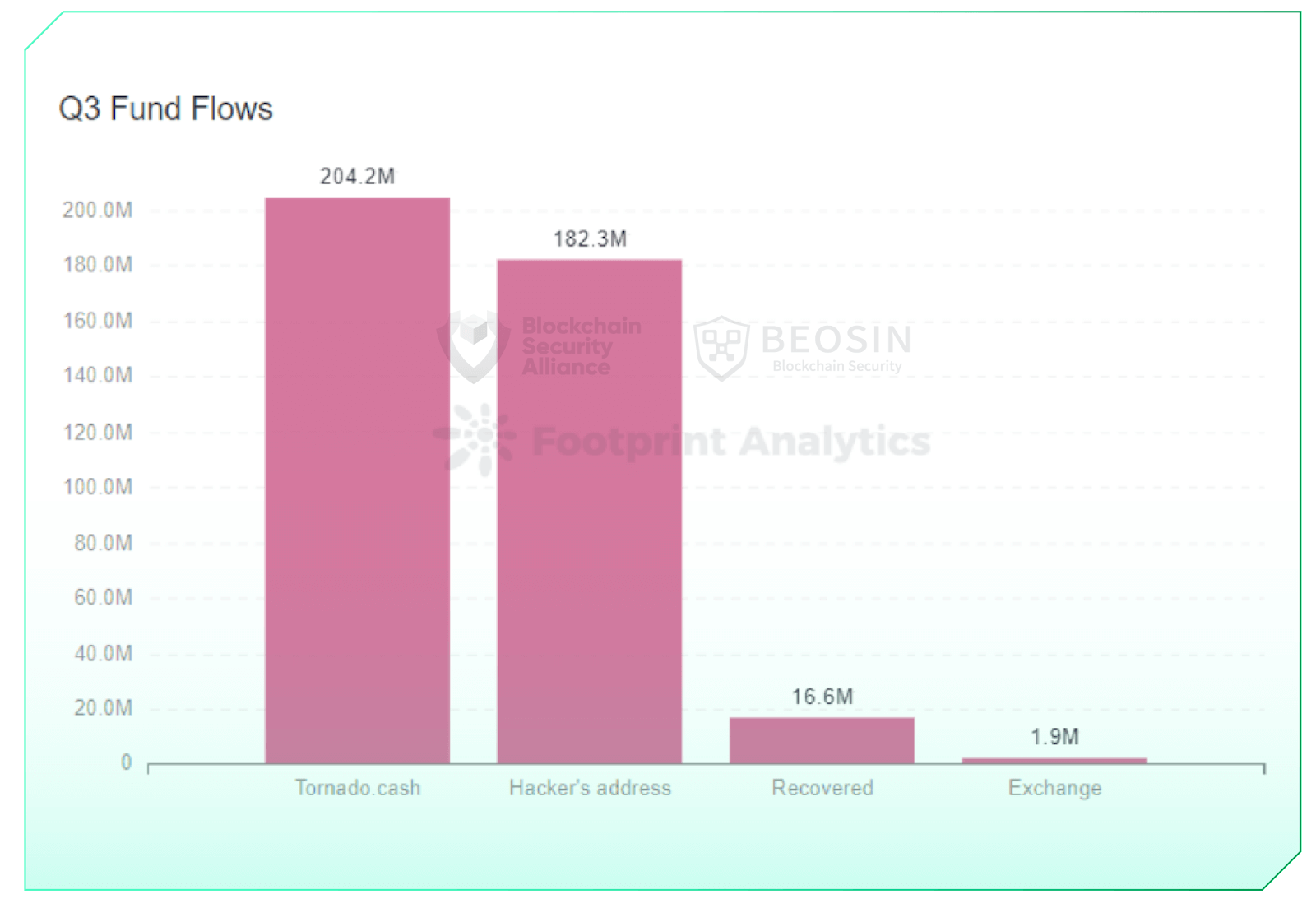
Regarding the flow of funds, Approximately $204.2 million of the stolen funds flowed into Tornado Cash, accounting for approximately 50.4% of the stolen funds during the quarter. Only about 4% of the stolen funds were recovered during the quarter.
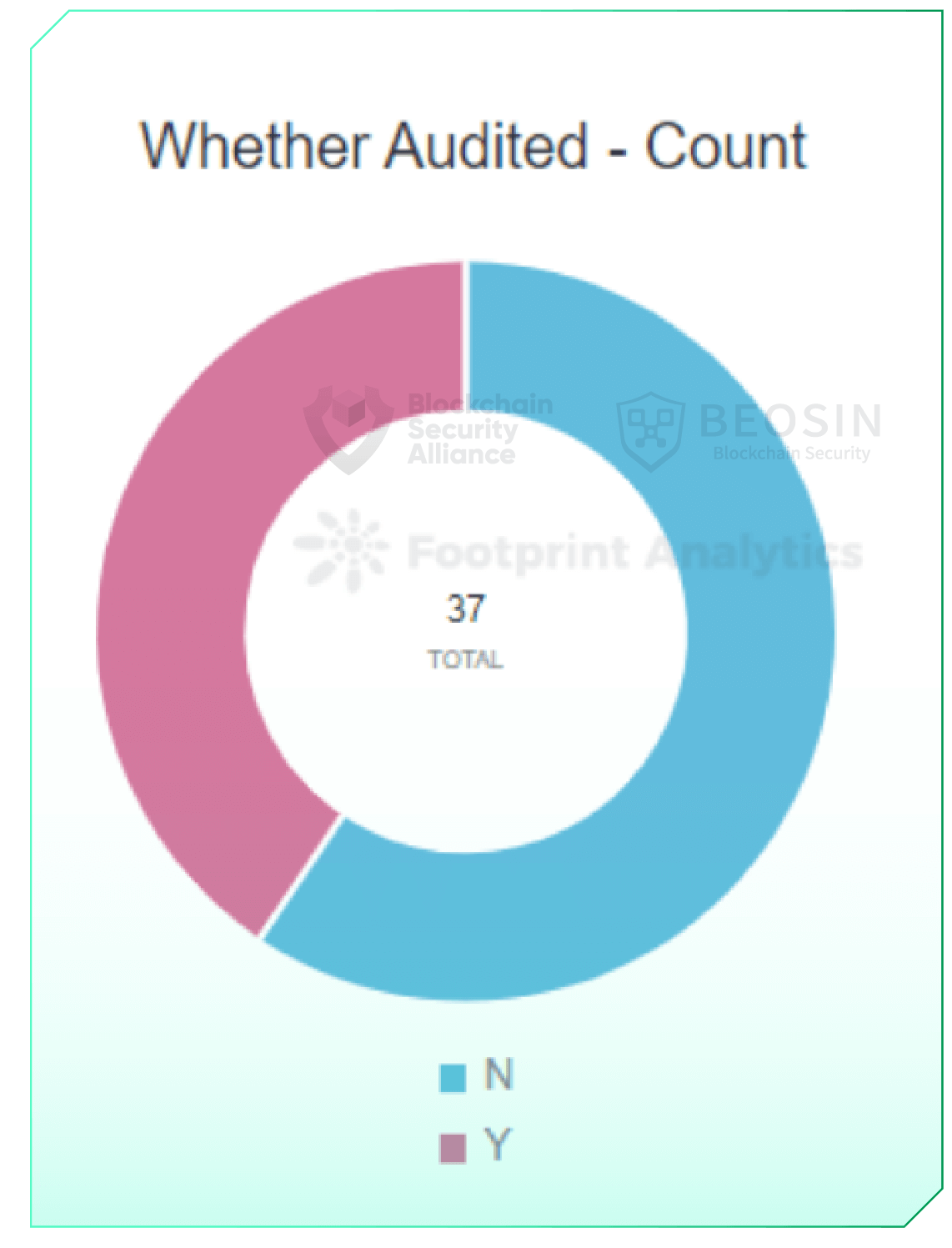
Regarding audits, Only 40% of rekt projects were audited.
2 Exploit overview
Overall attacks decreased in Q3 compared to Q2
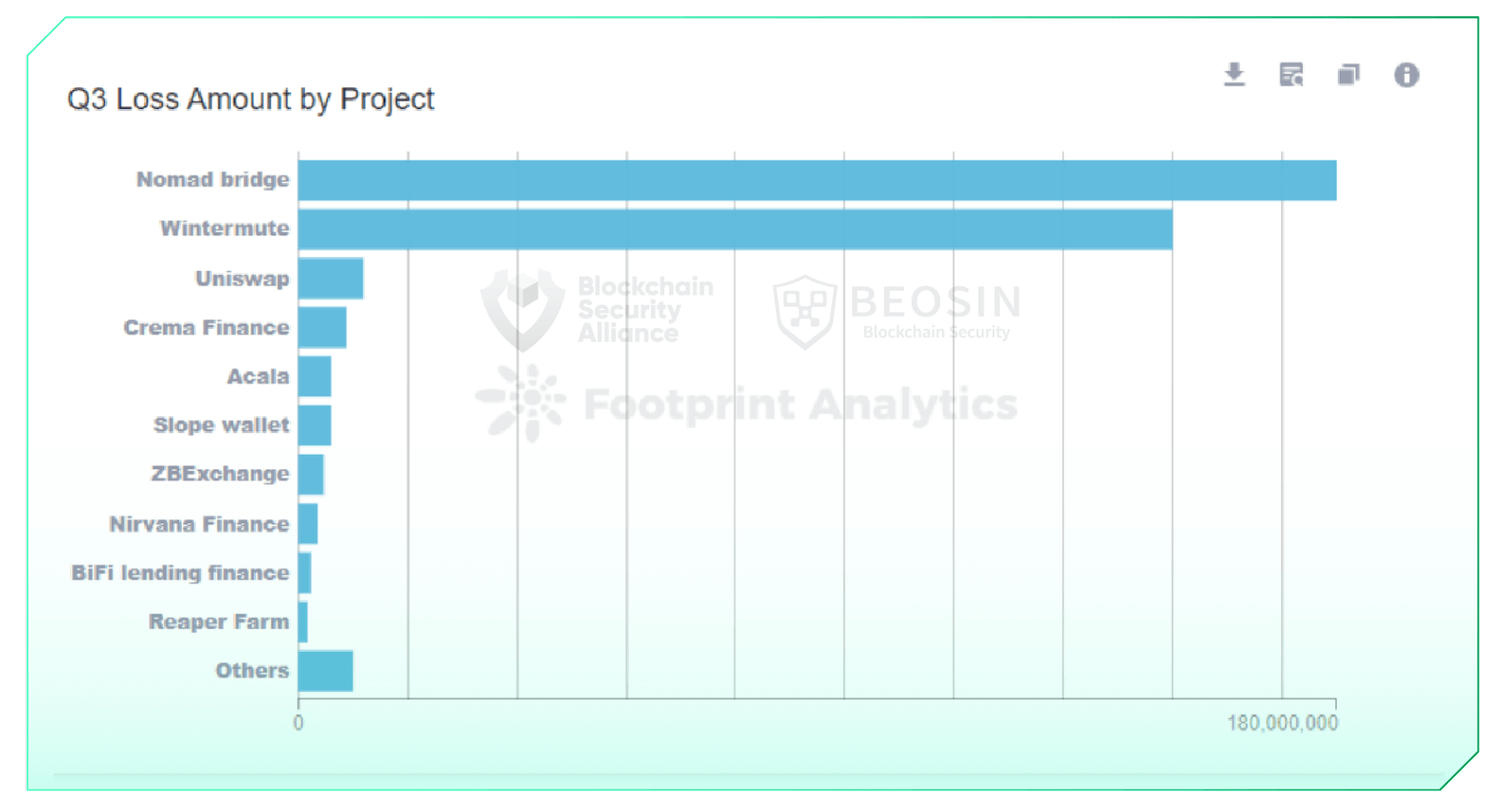
In Q3 2022, 37 large-scale attacks were observed in the Web3 space, resulting in a total loss of approximately $405 million. Two attacks resulted in losses of $100 million or more, three attacks resulted in losses of $10 million or more, and 14 attacks resulted in losses of $1 million or more. Security incidents with losses of $100 million or more nomad bridge ($190 million) and winter mute ($160 million).
August 2022 was the most active month for hackers in the quarter, with losses of approximately $210.62 million. His total loss from attacks in July was $30.05 million, the lowest loss in a month since 2022.
3 types of rekt projects
Cross-chain bridges and DeFi projects account for 92% of losses
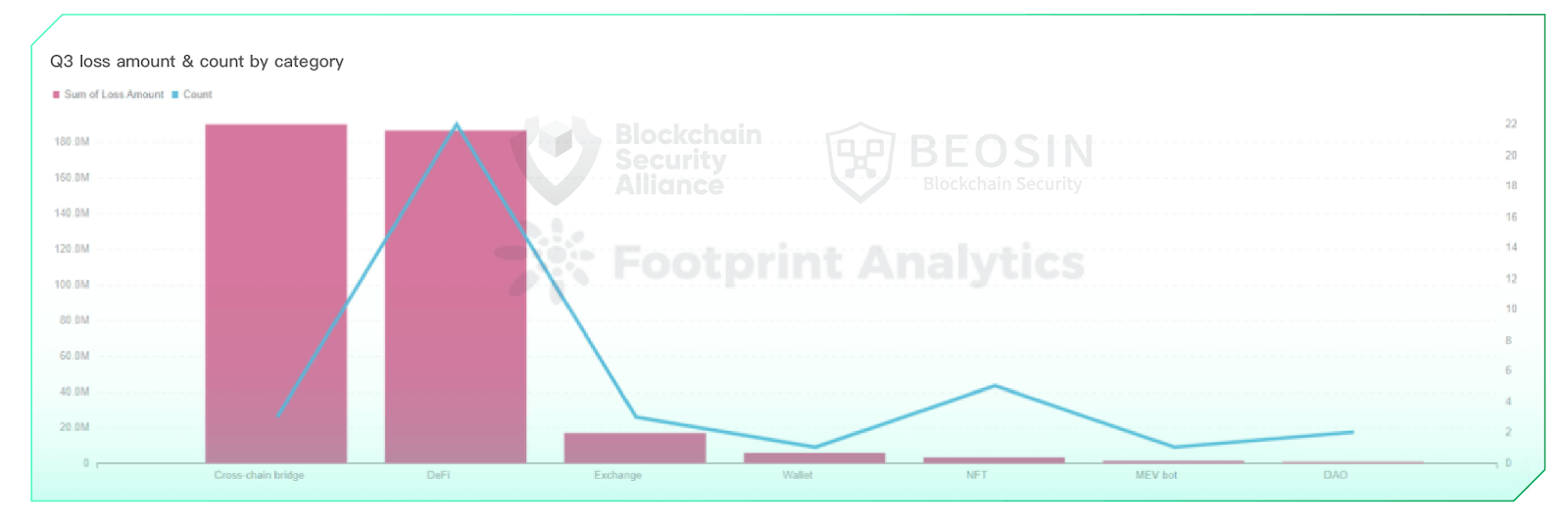
In Q3 2022, three cross-chain bridge attacks resulted in a combined loss of approximately $190.25 million. In total, his 22 attacks in the DeFi space cost him $186.79 million. About 92% of the attack losses were due to cross-chain bridges and his DeFi protocol.
As of September 2022, there will be 10 major cross-chain bridge security incidents in 2022, resulting in losses of over $1.4 billion. Cross-chain bridges were the areas most affected by attacks in 2022.
In addition to cross-chain bridges and DeFi protocols, other types of projects attacked this quarter included NFTs, exchanges, DAOs, wallets and MEV bots, with more types overall than last quarter. diversifying.
4 Loss amount by chain
Ethereum losses amount to $374.3 million
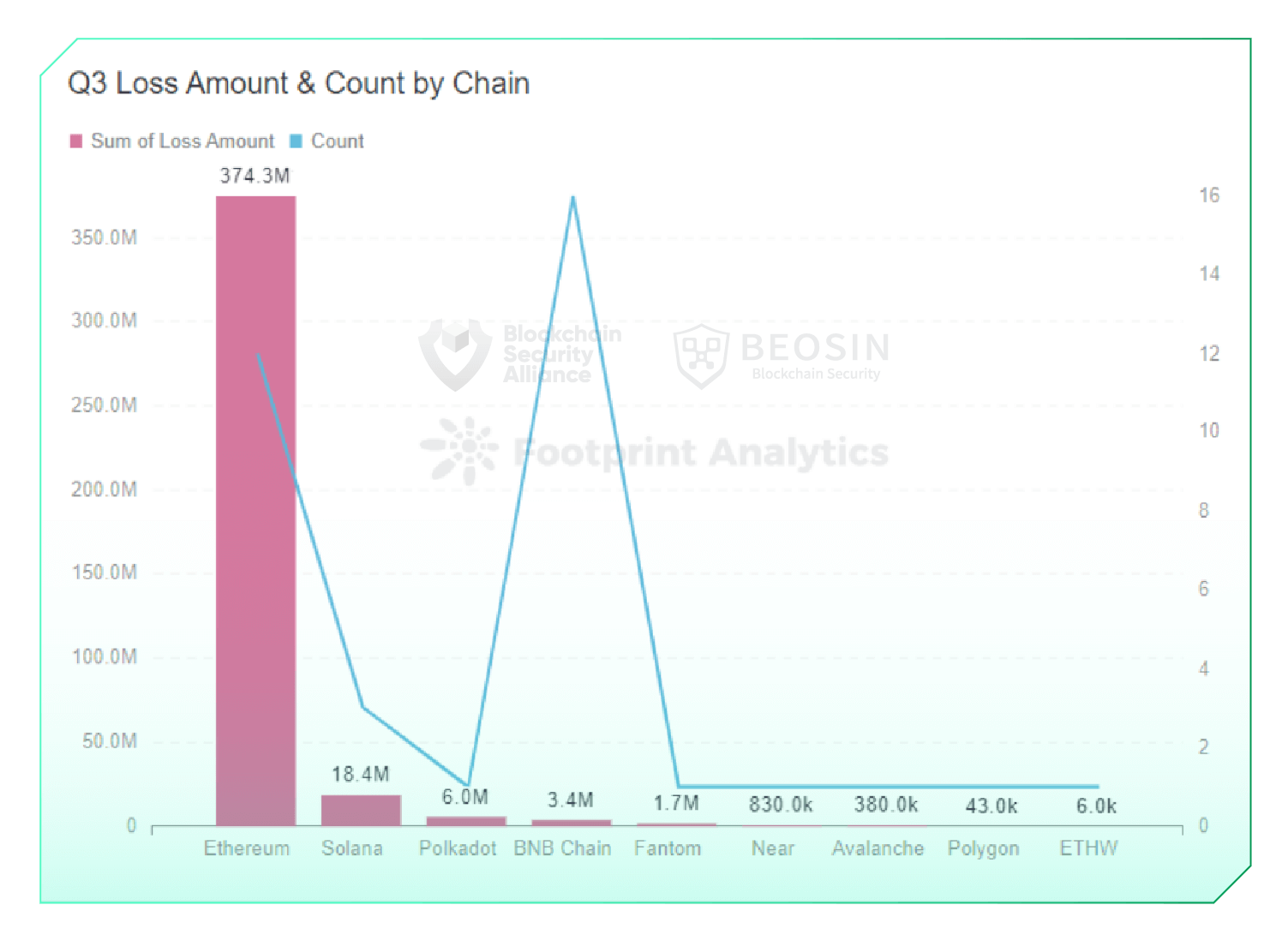
There were 12 large-scale attacks on Ethereum this quarter, resulting in a total loss of $374.28 million, ranking first among all chains. Solana lost her $18.37 million to her three exploits.
Chains that have been heavily attacked for two straight quarters include Ethereum, BNB chain, Phantom and Avalanche.
The BNB chain has seen the most attacks with 16 exploits and all corresponding projects are unaudited. The amounts involved in these 16 exploits were relatively small, with 14 incidents in which he lost less than his $500,000 on one occasion.
After a sharp drop in TVL in May and June, the chain-wide TVL trend stabilized this quarter. TVL he trended slightly higher in late July and early August, also during the quarter with the most attacks and losses. The cryptocurrency market fell slightly across the board in September. After the Ethereum merger on September 15th, Ethereum TVL continued to drop slightly.
5 Attack type analysis
92% of losses were due to contract vulnerability exploitation and private key compromise
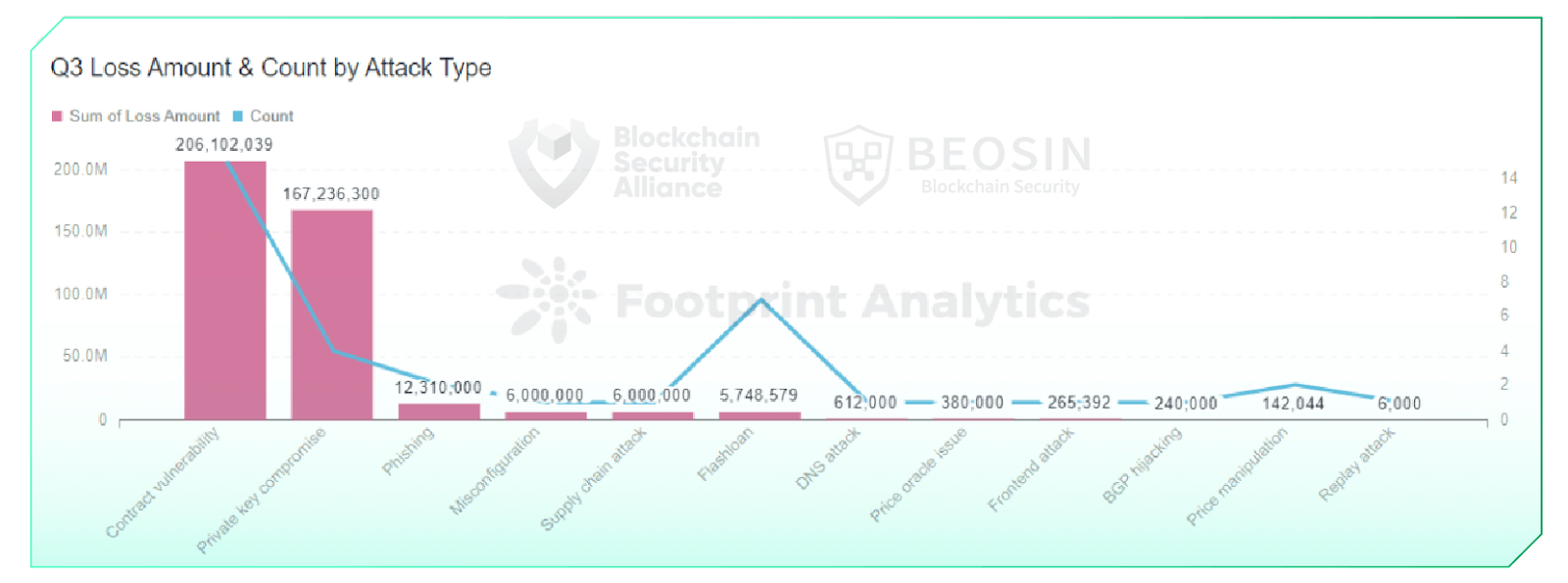
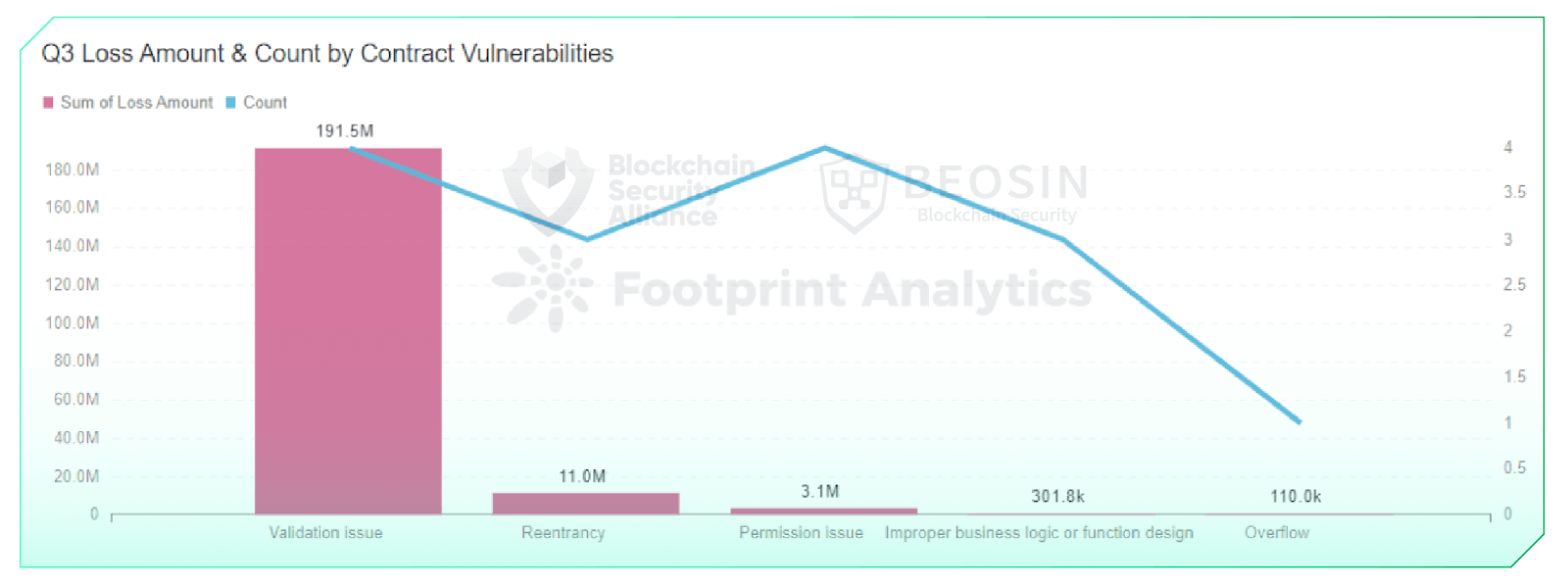
Contract exploits remained the most common attack type in Q3. About 15 attacks were contract vulnerability exploits, accounting for 40.5% of his total. Total losses due to contract vulnerabilities reached $201.6 million, or 50.9% of total losses.
Four private key compromises this quarter resulted in a loss of approximately $167.24 million. This is his second biggest loss after exploiting a contract vulnerability.
Compared to last quarter, the types of attacks this quarter are more diverse. New attack types that emerged this quarter included BGP hijacking, misconfiguration, and supply chain attacks.
According to Contract Vulnerabilities, the main vulnerabilities exploited this quarter included validation issues, reentrancy issues, permission issues, poorly designed business logic or functions, and overflow vulnerabilities. It is included. All of these vulnerabilities can be found and fixed during the audit stage.
6 Summary of typical security incidents
6.1 Nomad Bridge $190 million case
On August 2nd, Nomad Bridge, a cross-chain platform that supports asset transfers across Ethereum, Moonbeam, Avalanche, Evmos and Milkomeda, was hit by a massive hack that cost the project $190 million.
6.2 Slope Wallet incident in Solana
On August 3rd, a massive Slope wallet theft occurred on Solana, with an estimated loss of approximately $6 million.
6.3 Wintermute private key compromise incident
On September 20th, Wintermute, a cryptocurrency market maker, was hit with a $160 million loss due to compromised private keys.
7 Fund flow analysis
Approximately $204.2 million in stolen funds flowed into Tornado Cash
On August 8, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) sanctioned Tornado Cash, banning any U.S. person or entity from interacting with Tornado Cash. In the third quarter of 2022, approximately $204.2 million of stolen funds were still flowing into Tornado Cash.
About $182.3 million of the stolen funds remained at the hacker’s address. Some of the stolen funds have been bridged to addresses on other chains, and this portion still counts as the hacker’s address balance.
Approximately $16.6 million in assets were recovered through on-chain negotiations and unsolicited returns from white hat hackers. In the third quarter of 2022, only about 4% of the stolen funds were recovered. That’s a much lower percentage than in the second quarter.
About $1.92 million in stolen assets were leaked to exchanges such as Binance and FixedFloat. Incidents like this usually involve a small number of assets (usually about $10,000 to $100,000 for him), and the hacker transferred the stolen funds to an exchange shortly after the attack, so the project could have used the funds. The exchange could not be contacted in time to freeze.
8 Project audit analysis
Only 40% of projects were audited
The percentage of rekt projects audited in 2022 was 70% in Q1, 52% in Q2 and 40% in Q3. The percentage of unaudited rekt projects shows an increasing trend quarter by quarter.
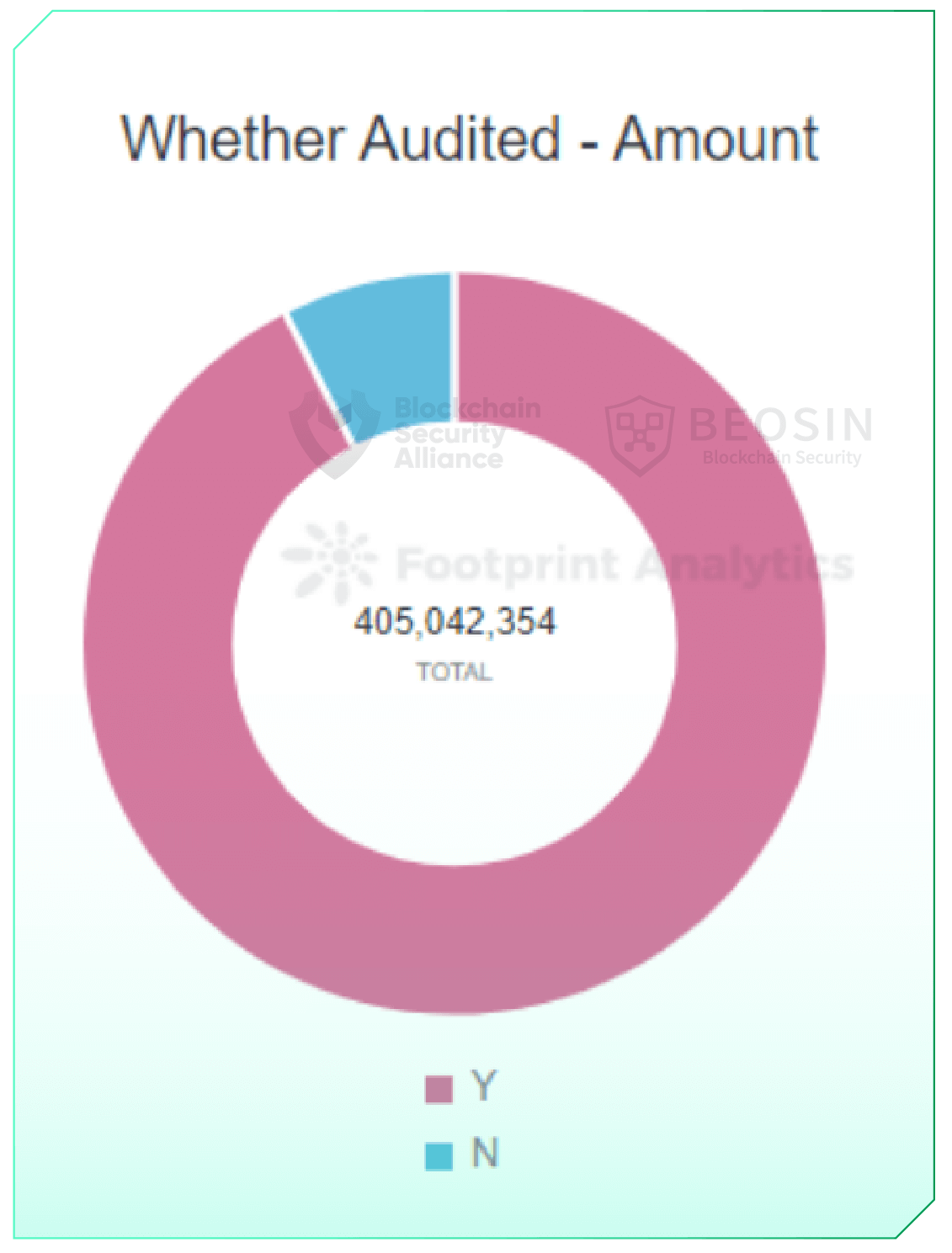
Of all rekt projects, audited projects lost a total of $375.48 million, while unaudited projects lost about $29.56 million to attacks. At first glance, it may appear that audits do not help safeguard the safe operation of projects. However, a more detailed analysis showed that most of these audited projects were attacked by non-contractual level issues such as private key compromise, supply chain attacks, DNS attacks, BGP hijacks, and misconfigurations. I’m here. 85% of unaudited projects were due to contract vulnerabilities or flash loan attacks.
Professional audits can still prove effective in securing projects to some degree at the contract level. However, operating the protocol securely also requires proper offline risk management, private key storage, vigilance against traditional network security attacks, and judicious use of third-party her components. Of course, there were some vulnerabilities in this quarter that should have been discovered during the audit phase, but didn’t show up in the audit report, so we recommend that the project be audited by a professional security firm. increase.
Download full version report:
About Blockchain Security Alliance
The Blockchain Security Alliance was launched by several units with diverse industry backgrounds, including academic institutions, blockchain security companies, industry associations, and fintech service providers. The Alliance Council’s first batch includes Beosin, SUSS NiFT, NUS AIDF, BAS and FOMO. Pay, Onchain Custodian, Semisand, Coinhako, ParityBit, Huawei Cloud. Current members include Huobi University, Moledao, Least Authority, PlanckX, Coding Girls, Coinlive, Footprint Analytics, Web3Drive, and Digital Treasures Center. Members of the Security Alliance work together to continuously secure the global blockchain ecosystem with their unique technological strengths. The Alliance Council also welcomes the participation of more people in blockchain-related fields to collectively secure the blockchain ecosystem.
Alliance registration
https://forms.gle/pb3NaUgS3a2Sswnc8
contact
Telegram: @kristenbeosin, @Web3Donny
Email: [email protected]
Alliance Member – Beocin
Beosin is a Singapore-based global blockchain security company with over 100 formal verification and blockchain security experts. With the mission of “protecting the Web3.0 ecosystem”, Beosin provides an integrated blockchain security product, including code security audit, risk monitoring, project warning and blocking, security compliance KYT and KYC, and stolen asset recovery. and provide services. Beosin currently provides security services to over 2,000 blockchain companies worldwide, audits over 2,500 smart contracts, and has protected over $500 billion in assets for clients. .
Alliance Members – Footprint Analysis
Footprint Analysis is a tool that reveals and visualizes data across blockchains, including NFTs and GameFi data. Now you can collect, parse, and cleanse data from 18 chains and create graphs and dashboards without code using a drag-and-drop interface or SQL or Python.





