CosmicStrand Malware Infects ASUS, Gigabyte Motherboards

Cosmic Strand is up to date A set of advanced malware that reaches a hardware bit seems to be much more difficult to compromise than a normal OS installation. But, as any cybersecurity researcher says, just because a breach is difficult doesn’t mean it’s unreachable. Researchers recently discovered a particularly nifty malware strand lurking on both ASUS and Gigabyte motherboards based on Intel’s H81 chipset. CosmicStrand has evolved since its first appearance in 2016, but at the moment it’s unclear if breakouts are limited to offering the larger motherboard markets of both companies, but there are darker revelations.
Researchers at Kaspersky Labs have discovered that malware is left behind in the Unified Extensible Firmware Interface (UEFI) (boot sector) of the motherboard. It is responsible for identifying, verifying, and booting all connected hardware bits. From simple fans to PC overclocking with the latest and greatest gaming CPUs, everything goes to your PC’s BIOS. For clarity, this is not the first such threat discovered-but one is already too many and adds to the possible infection vector.
The first thing to do in your system can be very difficult to remove malware through the BIOS before loading the antivirus solution into memory. It avoids most antivirus applications and cannot be removed with a fresh OS installation. It can also naturally withstand storage wipes, the three most common ways to remove security threats like these.
Things are especially troublesome if the malware can be deployed to the OS at the kernel level, that is, every boot. Remember, the kernel is the heart of the operating system and is responsible for the interface between the hardware and the high-level features of the operating system. Of course, all operating systems have protection against kernel tampering, but in this case Microsoft’s solution, ThreatGuard, is disabled by malware before it runs.
As Kaspersky’s analysis of malware shows, hijacking the kernel gives the malware control over the boot flow across the OS, prioritizing the process of reaching commands and control servers where the rest of the payload can be downloaded. Can be attached. .. Kaspersky estimates that this particular malware strand needs to be created directly for the motherboard BIOS. This doesn’t seem to be a kit over the internet.
So far, the infection seems to be limited to China, Vietnam, Iran and Russia. Kaspersky states that it has detected malware on three of its customers’ computers. All customers were running different versions of Kaspersky’s security software, and no one was a company, employer, or otherwise sharing a connection, adding a mystery to the purpose of the infection in the first place. ..
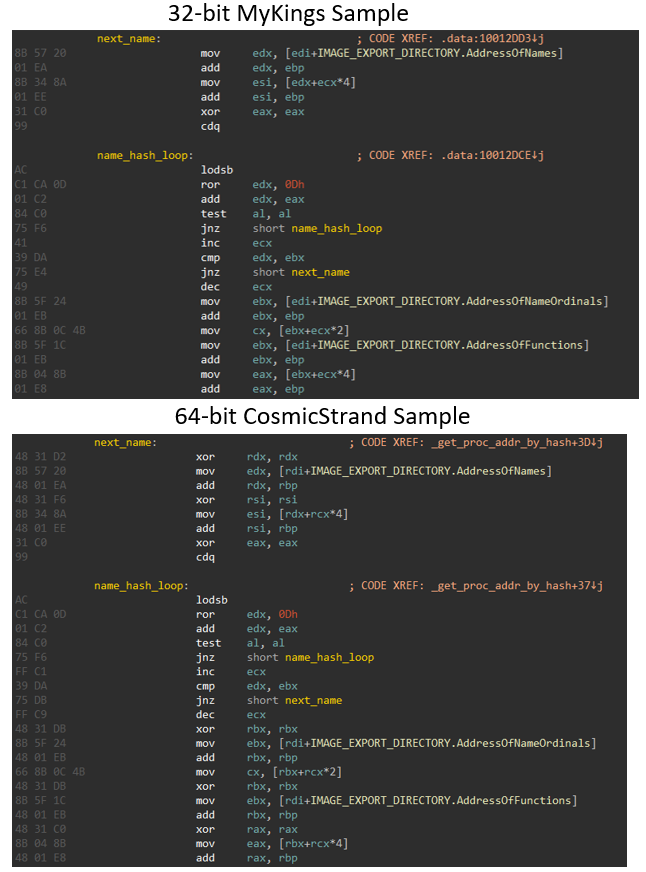
According to Kasperky’s analysis, the adapted CosmicStrand malware was created by a Chinese-speaking threat actor due to coding similarities with the payload that causes the MyKings botnet. Of course, this is not a black and white world. Chinese snippets may have been placed there to derail investigators. It takes more time (and perhaps more cases) to reach a definitive answer.
Kaspersky points out that the characteristics of Cosmic Strand reverted its creation in 2016. This is the time this infection vector slipped unnoticed. Currently, it is unknown how many other computers can be infected. As Kaspersky and other security providers focus on this threat, the number of infections can increase.
This also raises the question that BIOS malware may be lurking today, and it took years to further develop and refine previously unknown threats.
Cyber Security is a game of cats and mice between security researchers and threat actors. However, given what we know today about this particular malware infection and how it will be achieved, users are cautious about buying H81-based motherboards in the second-hand market. I can only suggest. In that case, don’t forget to always run an antivirus check. This is a good practice for PCs whose parts are built around hardware under the control of others.




