Security Expert Defeats Lenovo Laptop BIOS Password With a Screwdriver

Based in New Zealand, CyberCX’s cyber security experts consistently Accessing old laptops with locked BIOS. The linked blog post and video demo detail how a company executive used a simple screwdriver to short the pins of some of his EEPROM chips and access his fully unlocked BIOS. I’m here. After that, all I had to do was poke around in the BIOS setup screens and completely disable the BIOS password.
Before I go any further, it’s worth pointing out that CyberCX’s BIOS password bypass demonstration was done on a few retired Lenovo laptops. This blog shows an easily reproducible bypass that works on the Lenovo ThinkPad L440 (released Q4 2013) and the Lenovo ThinkPad X230 (released Q3 2000). Other laptop and desktop models and brands with different he EEPROM chips where passwords are stored can be vulnerable as well.
As some of you may know, there are many good used laptops sold as spares because they are BIOS-locked, making them virtually unusable. Individual owners and organizations may have neglected or forgotten to document these passwords. However, the system usually has the HDD or SSD removed as well, so it’s not worth as much as you might expect on the second-hand market. CyberCX pondered its old password-locked IT equipment and considered regaining full access to the hardware to use as a backup or test machine.
After reading various documents and research articles, CyberCX realized that the following process should be followed on BIOS-locked Lenovo laptops.
- Find the correct EEPROM chip.
- Locate the SCL and SDA pins.
- Short the SCL and SDA pins at the appropriate time.

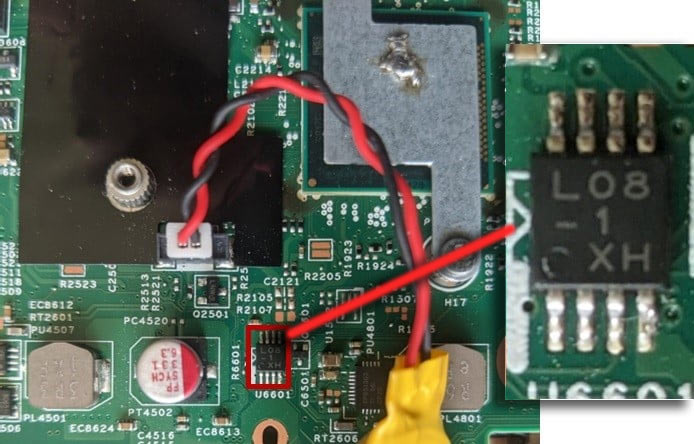
By checking the likely chips on the mainboard and looking at the series number, you will eventually be able to target the correct EEPROM. For the ThinkPad L440, the chip is marked L08-1 X (not always).
A video embedded in the CyberCX blog post shows how easy this “hack” is to perform. Shorting the L08-1 X tip pin requires a simple operation of pinching the tip of the screwdriver between his two tip legs. Once you enter the BIOS, you will see that all configuration options are modifiable. It is said that timing is necessary, but the timing is not that tight, so there is some leeway. Watch the video for a little “technique”.
CyberCX contains a fairly detailed analysis of how BIOS hacks work, and it is not possible to short the EEPROM chip immediately when the machine is powered on (hence the timing is required).
Some readers may be wondering about the laptops and BIOS-locked machines they see on eBay and elsewhere. According to Cyber CX, some modern machines with BIOS and EEPROM packages in his single surface mount device (SMD) are more difficult to hack this way and require an “off-chip attack”. It is said that it will be The cybersecurity firm also says that some motherboard and system makers are actually already using integrated SMDs. Those who are particularly concerned about their data and not their system should implement “full disk encryption”. [to] It prevents attackers from retrieving data from laptop drives,” said the security force.
CyberCX suggests continuing the above research. Perhaps we’ll look at whether it’s possible to read his BIOS password in plaintext from an EEPROM, or see if a driver hack is viable on more machines.




